
Cyber security for financial institutions is always a big focus, but the landscape grows even more challenging as the sector continues to evolve.
In 2020, 92% of financial service firms increased their cyber security investment in response to the new heightened risk from COVID-19 and digital transformation efforts.
In the face of new threats and challenges, having a comprehensive understanding of the emerging threats and risks means IT Managers can take the right measures in 2021.
Here are four of the biggest threats facing the sector and four actions IT Managers can take to prepare themselves for the new reality of financial services cyber security. Plus a free downloadable infographic summarizing the threats and how to respond.
The New Cyber Security Challenges You Need To Know – And How To Solve Them
Threat #1: Emerging Technologies
A survey by Deloitte and FS-ISAC found that for the last three years, rapid IT changes and rising complexities were the top cyber security challenge for financial firms. The push to innovate and evolve through digitalization has expanded the cyber-attack surface, creating new opportunities for attackers to leverage cutting-edge technology for malicious intent.
Financial institutions are using new technologies such as IoT, AI, robotic automation, 5G and cloud computing to develop new products, services and digital channels. But these new technologies can be just as harmful as they are helpful. They open doors to new attacks at unprecedented scale and speeds.
Action: Train Employees On Emerging Threats
Beat attackers at their own game by keeping a profile of emerging cyber security threats, trends and risks and regularly training your employees on how to handle them. Knowing how cyber-criminals are exploiting new technologies means threats can be addressed as soon as they emerge.
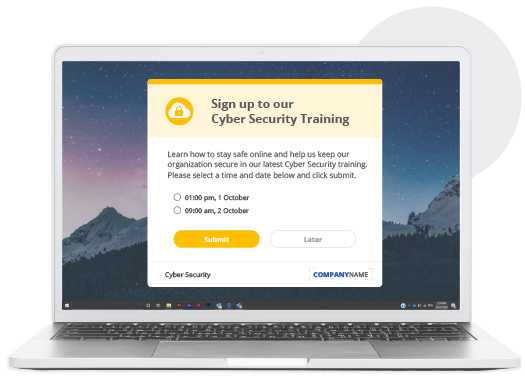
New attacks develop daily. Your approach to safeguarding your business against them can’t be limited to annual training. Schedule follow-up sessions at regular intervals to make sure that important information is retained. Use pop-up RSVP invites to maximize attendance at training sessions on new technology.
Employees should also be aware of their specific role in protecting information. Tailor training to simulate the unique threats different teams face and conduct interactive attack simulations to give employees hands-on experience where they need to react quickly.
Threat #2: New Operating Environments
COVID-19 has pushed many financial services firms to shift to remote working models, creating the perfect conditions for cyber-criminals to thrive. The pandemic sparked a 72% ransomware growth and a 50% growth in mobile vulnerabilities as the line between personal and corporate networks blurs.
Workers are stressed and distracted. Endpoints aren't secure, and remote access authentication is weak. Attackers have adapted their strategies to take advantage of the large attack surface of vulnerable work-from-home IT connections, pivoting towards phishing scams, malware and other tactics that exploit remote workers’ weaknesses.
Action: Reinforce Cyber Security Hygiene
90% of all cybersecurity attacks begin with human error. Increasing awareness of basic cyber security hygiene practices is one of the best steps IT Managers can take to safeguard operations in the age of remote work. It means employees can understand what cyber threats are and how to prevent them.
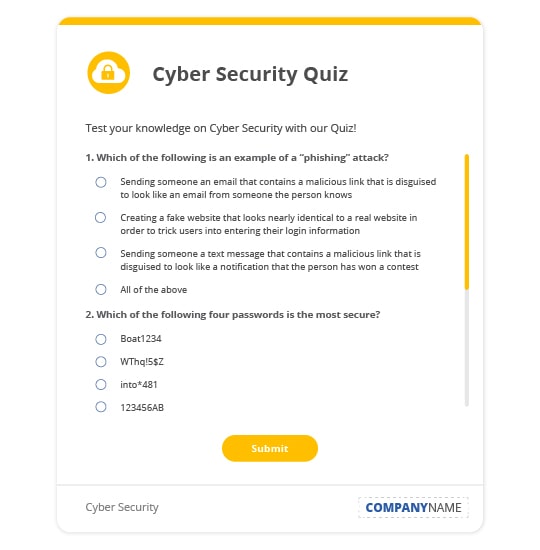
Quizzes can be used to enhance training and improve resistance to social engineering techniques. They’re particularly useful for segmented training that focuses on addressing how different teams experience different kinds of threats.
Threat #3: Yesterday’s Threats Have Evolved
As workplaces digitize, cyber-criminals are growing increasingly sophisticated and advanced in their attacks. Age-old threats such as phishing, ransomware and trojans are becoming increasingly automated, and tailored with personal information from company websites and social networks.
In the future, firms are likely to see a new trend in behavior as cyber-criminals shift their focus to spreading misinformation and changing or manipulating information, instead of just deleting or disrupting access to it. These attacks are harder to detect and have a longer recovery time as they manipulate data that firms use to plan, operate and grow.
Action: Enhance IT Communication
Fight misinformation with communication. Cybersecurity is more than just an IT function. To be effective it must take precedence in the minds of everyone at an organization. Ensure that there is strong communication around cyber security policies and guidelines around encryption, strong multifactor authentication and manual verification.
Make sure there are clear systems in place for alerting affected parties. Have ready-to-use IT Outage and Alert Templates in your back pocket so when disaster strikes you can act fast. Templated Alerts can reinforce IT security best practices and give employees tips on the type of negative online behavior they should avoid. It also means they have a clear way to distinguish genuine internal communication from false.
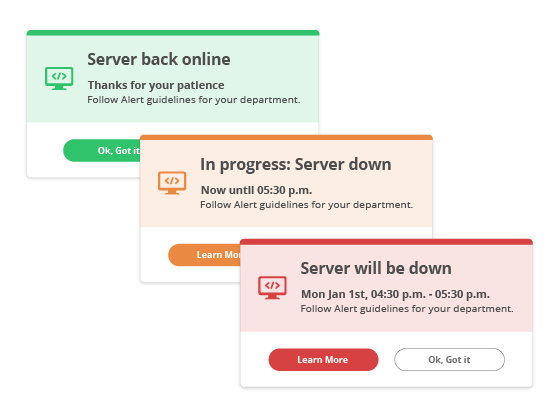
Your threats have evolved, so your communications need to as well. Use newsfeed-style Desktop Tickers to keep staff updated in real-time as the situation evolves. They bypass email completely to deliver urgent, unmissable messages with instant cut-through and maximum readership.

Threat #4: Attackers Exploit COVID-19
Thanks to COVID-19, online scammers are having a field day as they ramp up operations and alter tactics to exploit the pandemic. An Interpol report found more than 900,000 spam messages, 700 malware attacks and 48,000 malicious domains were using COVID-19 themed messaging to wreak havoc between January and April.
Some attacks lure unsuspecting employees with malicious emails promising COVID-19 medical packages and relief payments. Others pose as COVID-19 maps and even quizzes that test their knowledge of the pandemic to elicit passwords and account details for financial gain.
Action: Create A Culture Of Cyber Security
Forcepoint found that only 46% of leaders regularly review their cyber security strategies. Cyber security values and behaviors must be ingrained in an organization’s culture from top to bottom to successfully support cyber security and technology policies.
A culture of cyber security occurs when both the values and behaviors of leaders and employees align to support the wider cyber risk management strategy. So when anomalies arise, employees take the necessary precautions.
Leaders are essential in cultivating a risk-aware culture. They model the ideal behavior for an organization, as employees look to leadership to set the standard for cyber risk management. Video messages are a powerful tool to communicate the behavioral norms and desired values you’d like to ingrain in your cyber security culture.

Screensavers can turn idle computer screens into powerful messaging tools that raise the profile of authentication and verification policies. Reinforce the business risks that arise when the policy is not strictly followed.

The cyber security risk landscape is constantly evolving. Keeping up with the best ways to protect your business from emerging cyber threats is critical to minimizing risk and protecting your reputation.
For more tools to help you protect your business contact us now, or learn more about how the SnapComms platform can help you with your cyber security strategy.



